SCW Blog
Data privacy has never been such an important issue for businesses and individuals alike. In some places, calls for overarching legislation to protect consumers have often been met with significant pushback by lawmakers who are reluctant to put extra regulations on businesses, while others have passed important laws dictating how organizations handle individual data.
Encryption, like so many elements of cybersecurity, is often seen as just another buzzword that the public simply doesn’t need to concern themselves with… but as cyberattacks continue at their current rates, the opposite is the actual truth. Let’s talk about what encryption is, and why it has become more important than ever that it is put into practice in both professional and private life.
Data is commonly regarded as one of a business’ most valuable resources. As such, it is critical that you protect it from threats of all kinds, including data leaks. Data leaks are nothing to take lightly, as their impacts range from a serious hit to your business’ reputation to an equally serious hit to your business’ finances. Obviously, this is something to be avoided, so let’s discuss how you can do so.
Hackers and scammers are everywhere and are continuously littering your business with situations that could put its operations in jeopardy. One of the most hacked industries is healthcare, as hackers make a point at going after patient information. Let’s go through some of the reasons why hackers find health data so attractive.
Digital storage has been evolving with the development of reliable and long-lasting devices with extremely fast storage and massive storage capacity. The innovation of the solid state drive (SSD) has changed the outlook of storage somewhat, but large-capacity SSDs can be expensive. The hard disk drive (HDD) is still a cost-effective alternative, but it is a mechanical device, which, over time, will be prone to failure.
Most businesses leverage the cloud in at least some capacity, whether cloud-based apps or cloud-based infrastructure. In any case, using the cloud comes with inherent security questions that must be addressed during the planning, implementation, and launch phases of any solution. Let’s go over some of the ways you might protect data and applications stored in the cloud.
In our blog, we talk about security and data breaches all the time. We tell you how you can take efforts to avoid them and how to prepare your organization for the inevitability of being exposed to them. With all that security talk, we should briefly describe the difference between a security breach and a data breach, because they are two different things that get lumped together quite a bit.
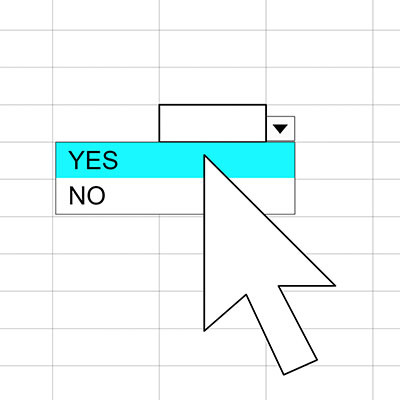
If you know how to use functions and various other features that Microsoft Excel and Google Sheets have to offer, then you can take your skills one step further than most. One such feature is the use of dropdown menus within cells. Let’s discuss how you can use them to your benefit in both Excel and Sheets.
We know that security is far from a small investment, but this only serves to highlight how important it can be to your business’ continued success. You might wonder why security is such an important investment if you don’t intend to suffer a data breach, and that’s precisely the point. The cost of not investing in security far outweighs the initial investment.
We bet you’ve gone through your old files at some point to clean things up a bit by deleting files from your computer. What if we told you that deleting those files doesn’t actually delete them—at least not entirely? Let’s go over how you can securely delete your files for good while you go about replacing hardware or upgrading your technology systems.
There’s no getting away from streaming nowadays—if you’re not binging something on Netflix/Hulu/HBOmax (etc, etc), you’re listening to your favorite song on your music platform of choice. This is largely due to the rising popularity of the “as-a-service” strategy that cloud services enable nowadays. Let’s take a closer look at streaming, and why it is now so ubiquitous.
For years you’ve heard how technology is becoming a bigger part of the healthcare delivery system and how it can help stabilize costs, provide increased access, and further personalize care delivery. As these innovations have been taking hold it has brought up serious questions about data privacy. Today, we’ll take a look at some of the changes IT has brought to healthcare and what it means for patient data privacy.